An IP Address is the foundation of internet communication and cybersecurity. Every device connected to a network uses IP to identify itself, send data, and receive responses.
Without an IP Address, devices cannot communicate across networks, access websites, or connect to cloud services. In enterprise cybersecurity, monitoring IP activity helps detect cyber attacks, unauthorized access, and malicious traffic.
This Tech Naga guide explains IP Address architecture, real-world examples, NAT, enterprise implementation, interview questions, and future trends for 2026. moreinfo
Definition of IP Address
An IP Address is a unique numerical identifier assigned to every device connected to a network. It enables:
- Device identification
- Network location
- Data communication
- Internet routing
Example:
192.168.1.10
Think of an IP Address like a home address for your computer.
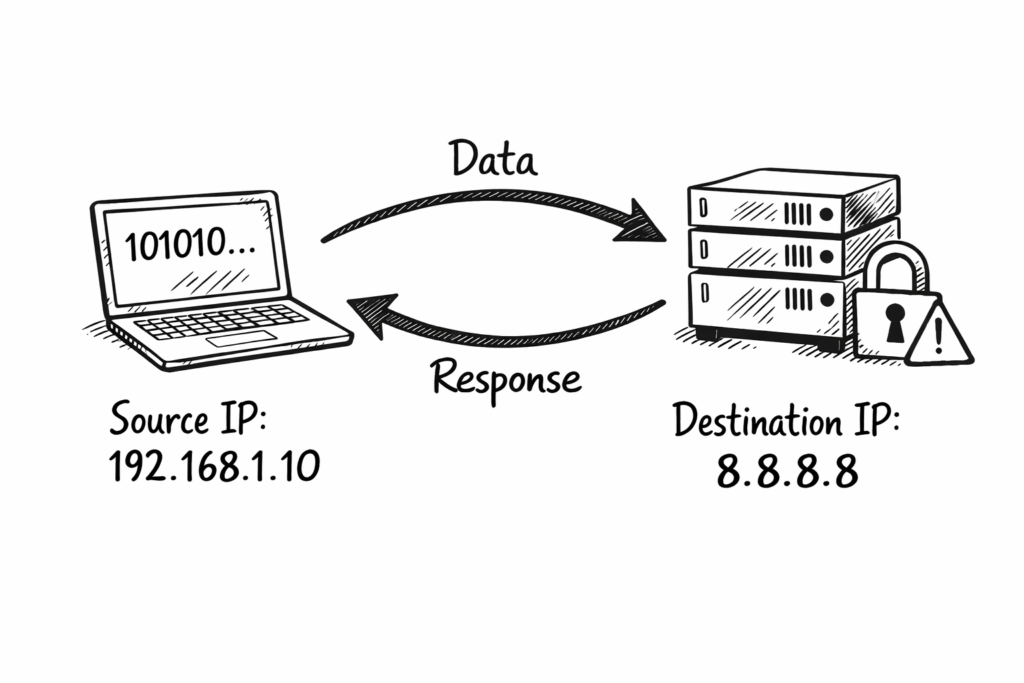
How IP Address Works
When a user opens a website, their system sends a request containing its IP Address. The destination server uses this IP Address to send the correct response back.
Routers examine source and destination IP Address information inside packets. Based on routing tables, routers forward packets through the best available path until reaching the destination device successfully and securely.
This process happens within milliseconds globally. Millions of devices communicate simultaneously using IP Address, making internet communication fast, reliable, scalable, and efficient across different countries, networks, and infrastructure environments.
When you open a website like Google:
Step-by-Step Process
Step 1: Device sends request
Source IP: 192.168.1.10
Destination IP: 142.250.183.14
Step 2: Router forwards packet
The router checks the routing table and forwards traffic.
Step 3: Firewall inspects traffic
Firewall allows or blocks traffic based on policy.
Step 4: Server responds
Server sends response to your IP Address.
This entire process takes milliseconds.
Structure of IP Address
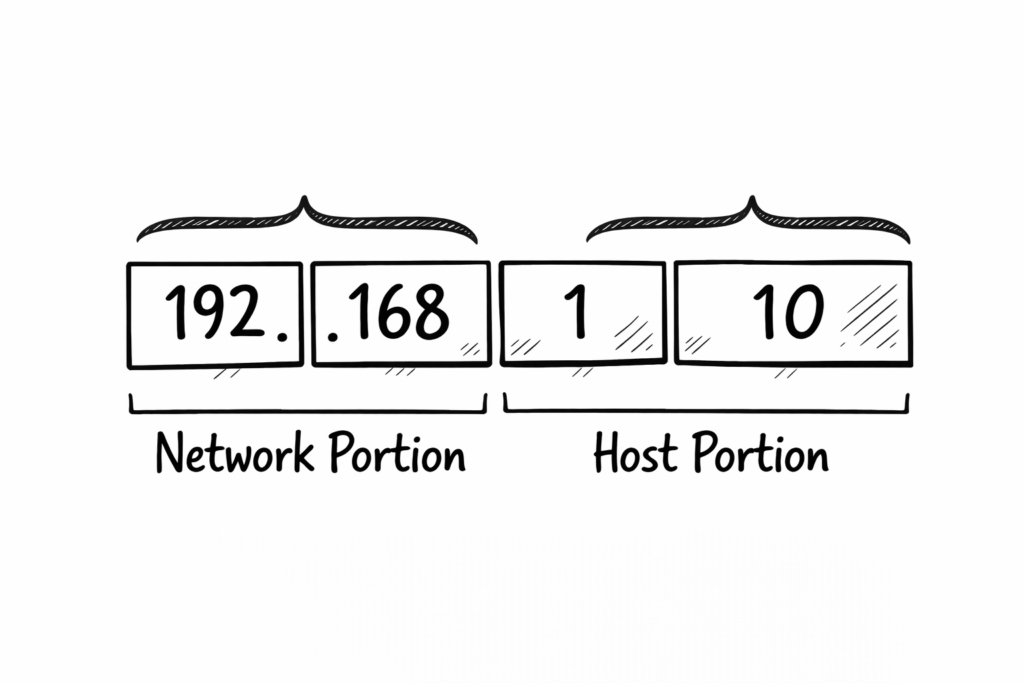
An IPv4 IP Address contains four numbers separated by dots. Each number ranges from zero to two hundred fifty-five. This format helps network devices identify network and host portions.
Examples of IPv4 IP Address include 192.168.1.10. Here, the network portion identifies the network, and the host portion identifies specific devices. Subnet mask determines how network and host portions divide exactly.
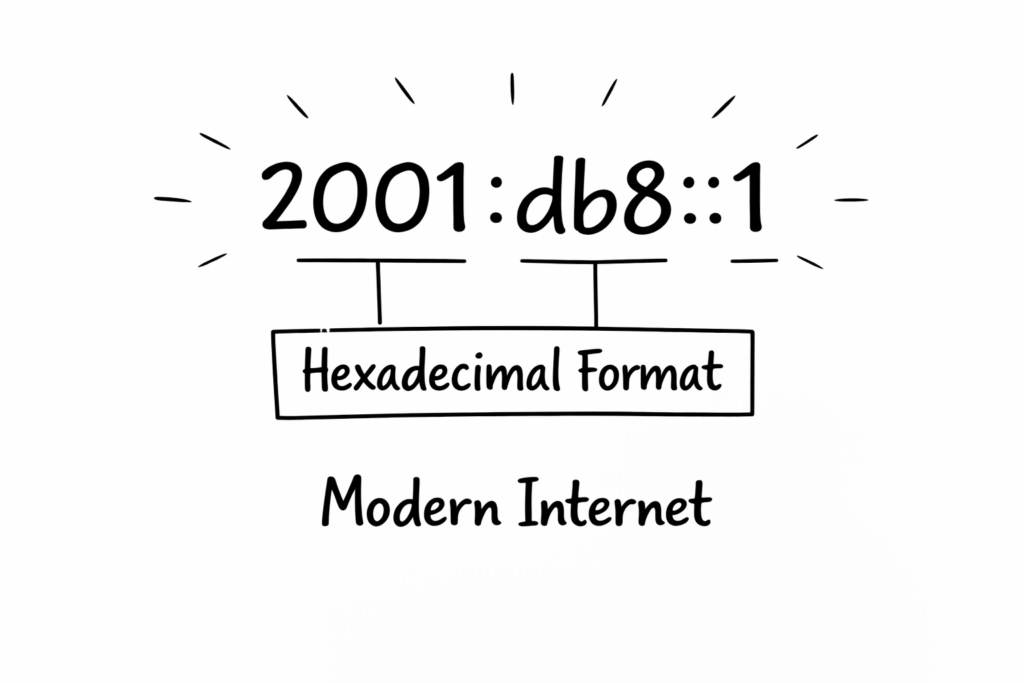
IPv6 IP Address uses hexadecimal format separated by colons. It provides massive address space supporting billions of devices, making it future-ready for cloud computing, IoT, and enterprise networking environments.
IPv4 Structure
Example:
192.168.1.10
Features
- 32 bits
- 4 octets
- Decimal format
Breakdown
| Part | Example | Purpose |
| Network | 192.168 | Network identification |
| Host | 1.10 | Device identification |
IPv6 Structure
Example:
2001:db8::1
Features
- 128 bits
- Hexadecimal format
- Supports billions of devices
IPv6 solves IP Address shortage.
Types of IP Address
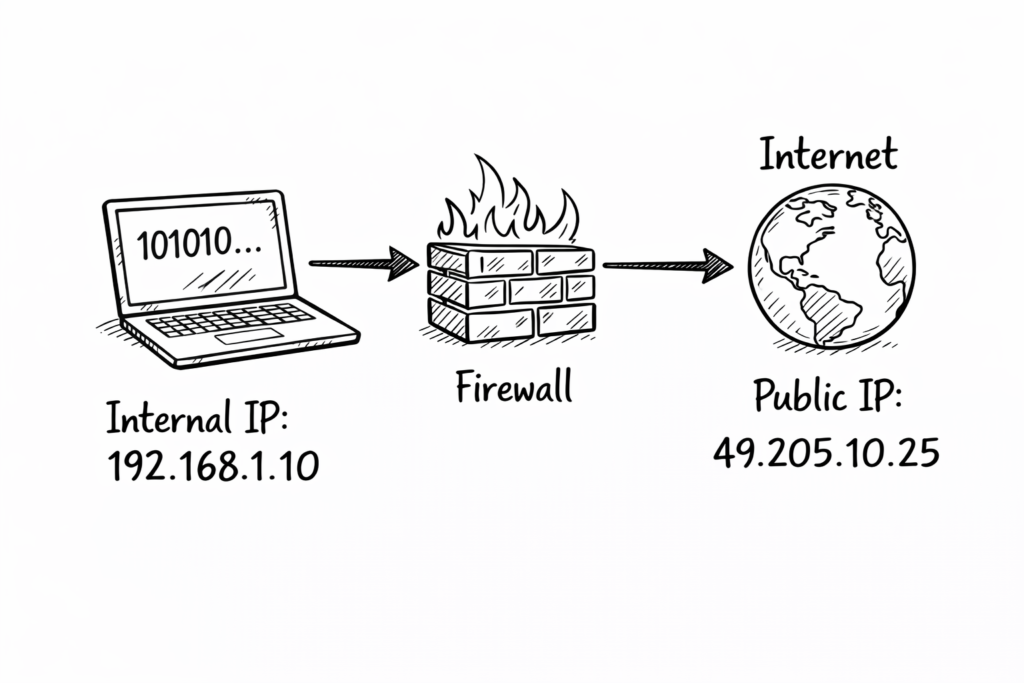
Public IP Address is assigned by internet service providers. It is globally unique and allows devices to communicate directly with internet servers, websites, and cloud services worldwide securely.
Private IP Address is used inside local networks such as offices and homes. It cannot communicate directly with the internet without NAT translation performed by firewall or router.
Static IP Address remains permanent and does not change automatically. It is commonly used for servers, firewall management, and applications requiring constant connectivity and stable network identification purposes.
Dynamic IP Address changes automatically using DHCP server. It is commonly assigned to user devices like laptops and mobiles to simplify network management and reduce administrative configuration overhead.
Public IP Address
Used on the internet.
Example:
49.205.10.25
Assigned by ISP.
Private IP Address
Used inside LAN.
Example ranges:
- 192.168.x.x
- 10.x.x.x
- 172.16.x.x
Used internally.
Loopback IP Address
Example:
127.0.0.1
Used for testing.
Public vs Private IP Address
Private IP Address
Used inside a company network.
Example:
10.10.10.5
Cannot access the internet directly.
Public IP Address
Used outside the network.
Example:
103.25.100.5
Accessible globally.
Why Private IP is used?
Benefits:
- Security
- Cost saving
- IP conservation
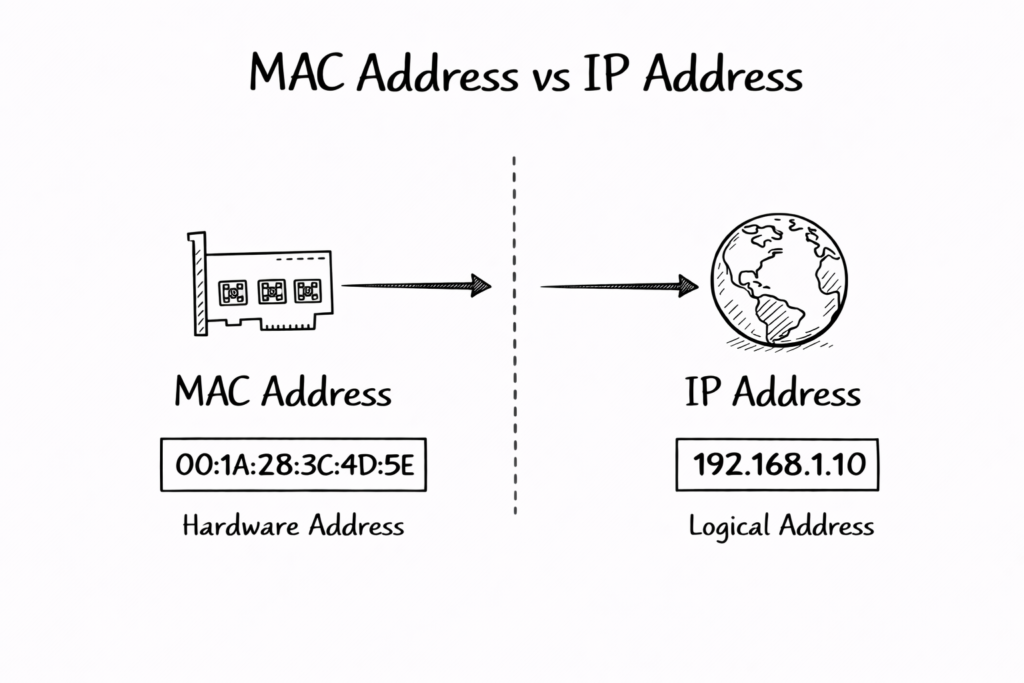
MAC Address vs IP Address
Definition
MAC Address: Physical address of device.
IP Address: Logical address of device.
MAC Address is the physical address assigned to a network card by the manufacturer. It identifies devices within the local network and operates at Layer two of the OSI networking model.
IP Address is a logical address assigned by a network administrator or DHCP server. It identifies devices across different networks and operates at Layer three of the OSI networking model.
MAC Address never changes normally, but IP Address can change depending on the network. Both MAC Address and IP Address work together to enable successful communication between devices globally.
Key Differences
| Feature | IP Address | MAC Address |
| Layer | Layer 3 | Layer 2 |
| Type | Logical | Physical |
| Change | Yes | No |
| Example | 192.168.1.10 | 00:1A:2B:3C:4D:5E |
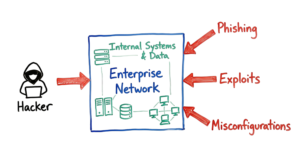
Enterprise Architecture Explanation
Enterprise Network Components
Typical enterprise network includes:
- User Laptop
- Switch
- Firewall
- Router
- Internet
Real-World Enterprise Example
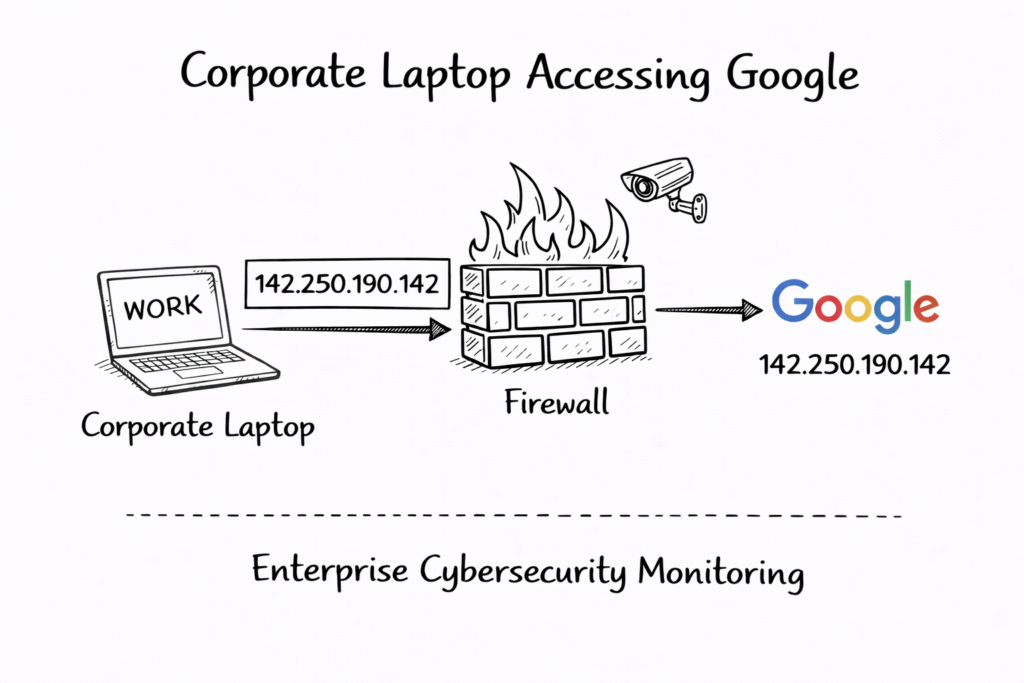
In corporate environment, user laptop receives private IP Address like 10.10.10.5. Firewall translates it into public IP Address before allowing internet access through secure NAT translation process.
Firewall logs record IP Address activity for security monitoring. Cybersecurity teams analyze IP Address logs to detect malicious traffic, unauthorized access attempts, and potential data breach indicators quickly.
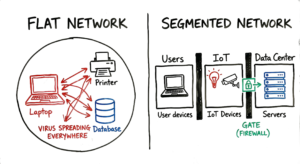
Companies implement IP Address-based access control policies. Only authorized IP Address ranges can access sensitive applications, servers, and management systems, improving overall enterprise security posture significantly.
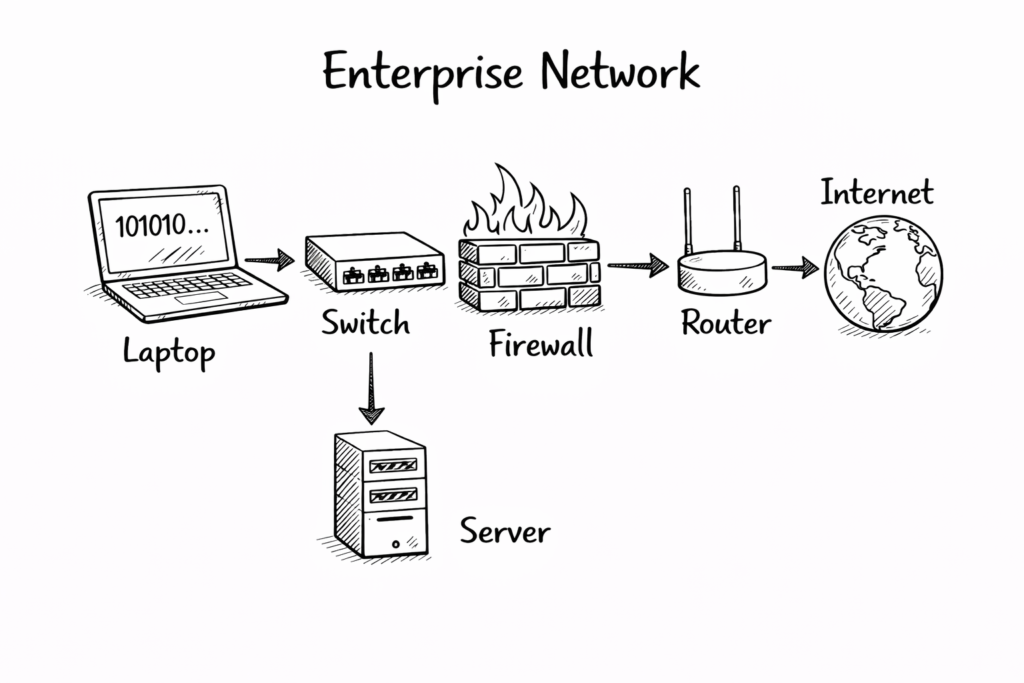
Architecture Flow
User Laptop → Firewall → Router → Internet → Server
Firewall monitors IP Address traffic.
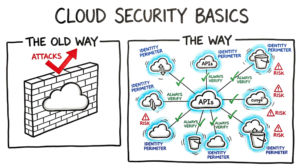
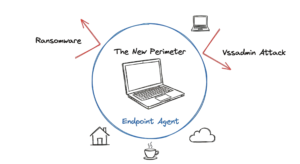
Cybersecurity Importance
Security tools like firewall, SIEM, and antivirus monitor IP Address traffic. Suspicious IP Address connections trigger alerts, allowing security teams to investigate and prevent cyberattacks effectively immediately.
IP Address helps identify attacker location, source, and behavior patterns. Security analysts use IP Address intelligence to block malicious IP Address and protect organization infrastructure proactively.
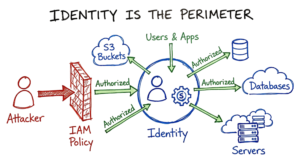
Zero Trust security model uses IP Address as one of identity factors. Combined with authentication and device verification, IP Address helps enforce strong access control policies everywhere.
Security teams monitor:
- Source IP Address
- Destination IP Address
- Threat IP Address
Used in:
- SIEM
- Firewall logs
- Zscaler
- Endpoint security
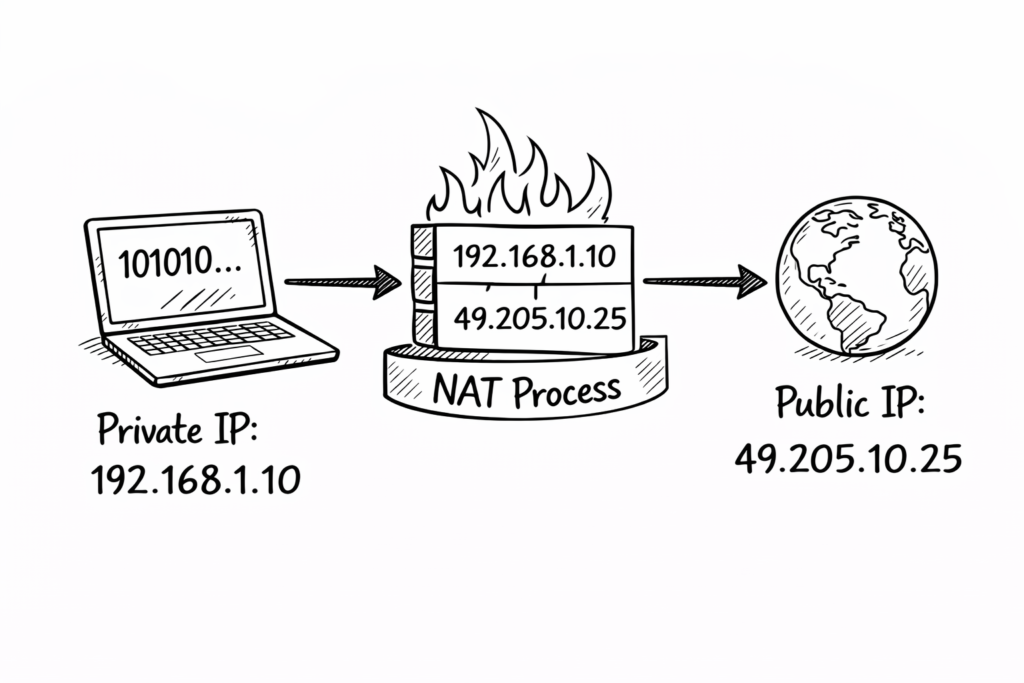
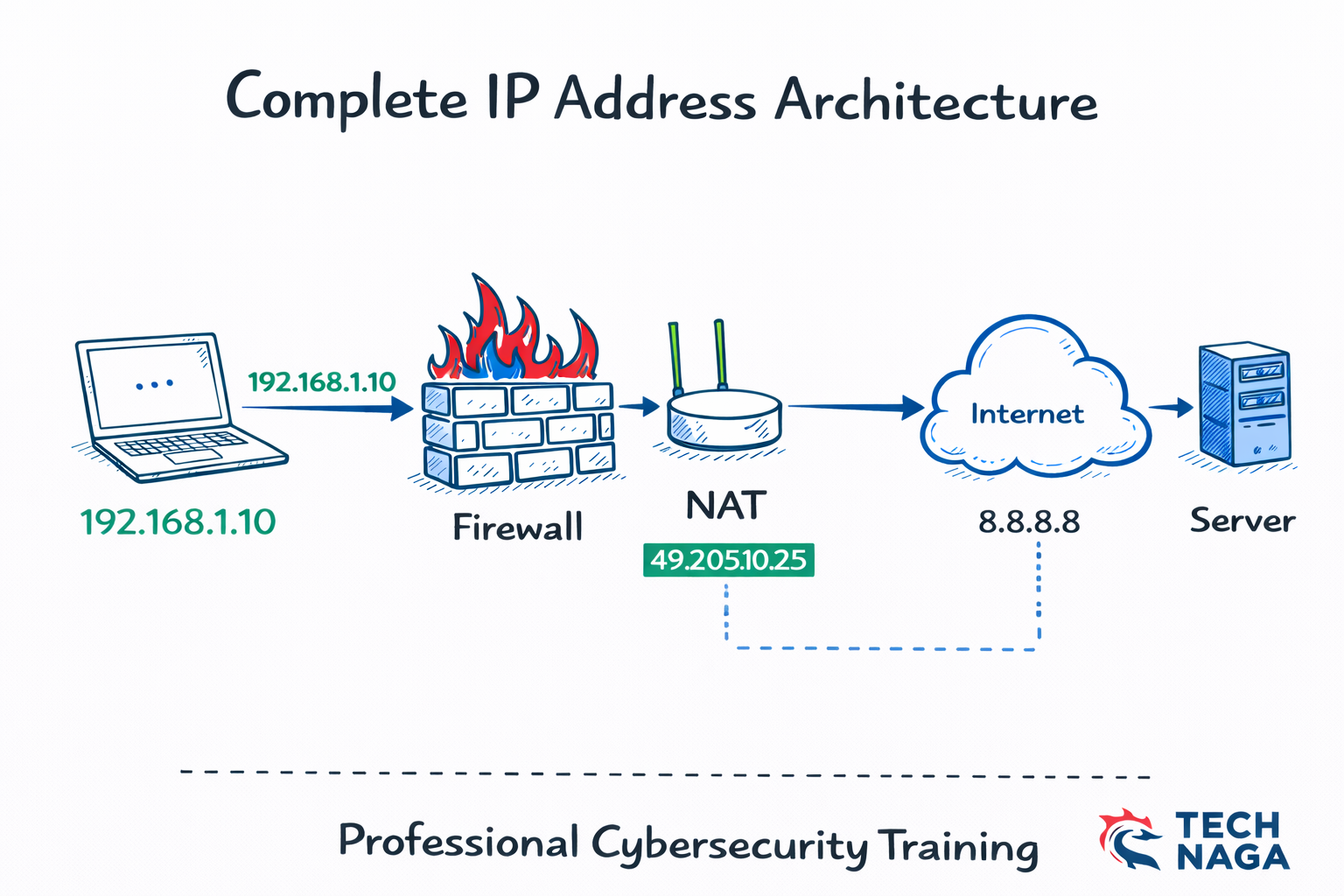
NAT and IP Address Translation
What is NAT
Network Address Translation converts private IP Address into public IP Address. This allows multiple internal devices to share a single public IP Address while accessing the internet securely and efficiently.
Firewall maintains a translation table mapping private IP Address and public IP Address. When the response returns, the firewall forwards traffic to correct internal devices using IP Address mapping information.
NAT improves security because internal IP Addresses remain hidden. Attackers cannot directly access private IP Address, reducing risk of unauthorized access and improving enterprise network protection significantly.
NAT converts private IP Address into public IP Address.
Example:
Private IP:
192.168.1.10
Converted into:
49.205.10.25
Why NAT is required
Benefits:
- Security
- Hide internal network
- Save IP addresses
Where NAT happens
NAT configured on:
- Firewall
- Router
Example:
Firewall like Palo Alto Networks firewall performs NAT.
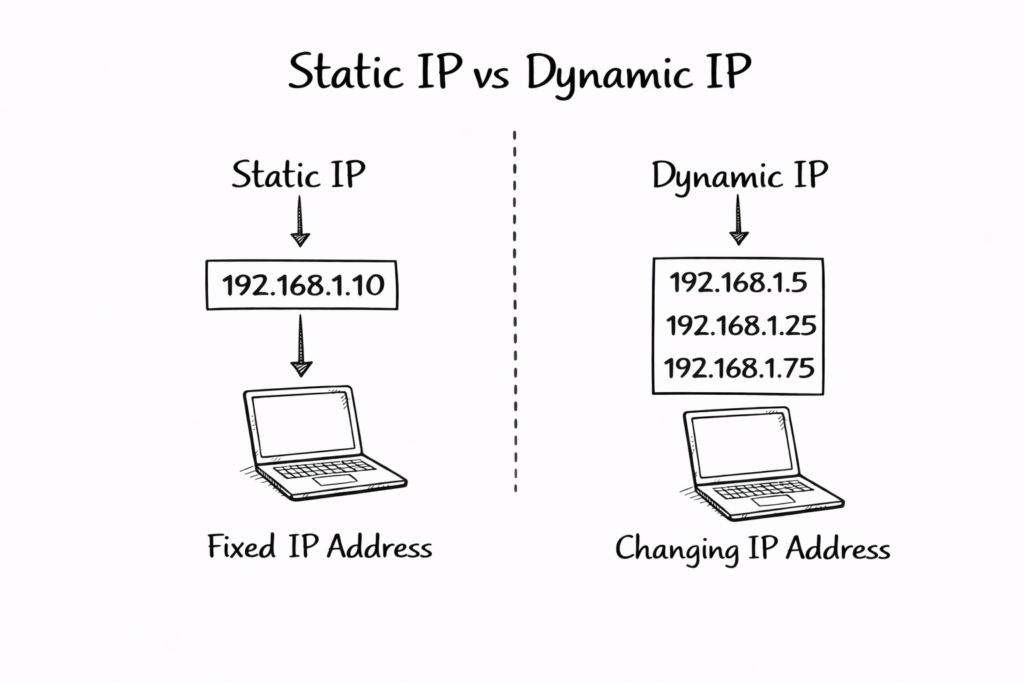
Static vs Dynamic IP Address
Static IP Address
Fixed IP.
Used for:
- Servers
- Firewall
- Printers
Example:
10.10.10.5
Dynamic IP Address
Changes automatically.
Assigned by DHCP.
Used for:
- Users
- Laptops
Example:
192.168.1.20
Real-World Enterprise Example
Corporate Network Example
Company: Tech Naga Pvt Ltd
Laptop IP:
10.10.10.5
Firewall Public IP:
103.25.100.5
Traffic Flow
Step 1:
Laptop sends request
Step 2:
Firewall converts IP using NAT
Step 3:
Internet sends response
Step 4:
Firewall logs IP Address
Security Monitoring
Security team monitors:
- Malicious IP Address
- Unknown IP Address
- Suspicious IP Address
Using tools like:
- SIEM
- Microsoft Defender
- Cloudflare security
Advantages and Disadvantages of IP Address
IP Address enables communication between devices across the internet and networks. Without IP Address, global connectivity, cloud computing, and online services would not function properly today.
IP Address helps network administrators monitor, manage, and troubleshoot network problems. Logs and monitoring tools use IP Address to identify issues quickly and resolve efficiently.
IP Address supports scalability of the internet. Millions of devices connect daily, and IP Address ensures each device communicates correctly without conflict or communication errors globally.
Advantages
1. Communication
Devices communicate using IP Address.
2. Identification
Identifies devices.
3. Security Monitoring
Helps detect attacks.
4. Routing
Helps data routing.
Disadvantages
1. Can be tracked
Attackers track IP Address.
2. Security risk
Public IP Address exposed.
Common Mistakes
Using the wrong subnet mask can break communication. Incorrect subnet configuration prevents IP Address from reaching the correct network, causing connectivity failure and application access problems frequently.
Exposing a public IP Address without firewall protection increases security risk. Attackers can target exposed IP Address using scanning tools and exploit network vulnerabilities easily.
Not monitoring IP Address logs reduces security visibility. Organizations may miss suspicious activities, allowing attackers to remain undetected and cause damage over time silently.
Mistake 1: Wrong subnet mask
Causes network issues.
Mistake 2: Exposing public IP Address
Security risk.
Mistake 3: No monitoring
Leads to cyber attacks.
Best Practices
Best Practice 1: Use Private IP internally
Improves security.
Best Practice 2: Use firewall
Protect network.
Best Practice 3: Use NAT
Hide internal IP Address.
Best Practice 4: Monitor IP logs
Detect threats.
Interview Questions and Answers
Question 1: What is an IP Address?
Answer:
IP Address identifies devices on the network.
Question 2: Difference between public and private IP Address?
Answer:
Public IP used on the internet.
Private IP used internally.
Question 3: What is NAT?
Answer:
NAT converts private IP Address into public IP Address.
Question 4: Why is IP Address important in cybersecurity?
Answer:
Used to monitor threats.
Question 5: What happens when a user opens a website?
Answer:
Request sent using IP Address.
Future Trends 2026
1. IPv6 Adoption
IPv6 is increasing.
2. Cloud Networking
Cloud uses IP Address.
3. Zero Trust Security
Uses IP monitoring.
4. AI Security
AI analyzes IP Address traffic.
FAQ Section
What is an IP Address example?
Example:
192.168.1.1
Can IP Address change?
Yes.
Dynamic IP Address changes.
Is an IP Address unique?
Yes.
Each device has a unique IP Address.
Why is an IP Address used?
For communication.
Conclusion
An IP Address is the foundation of modern networking, cybersecurity, and internet communication. Every device connected to a network relies on an IP Address for identification, routing, and secure data transmission across local networks, enterprise environments, and the global internet.
Understanding how an IP Address works enables professionals to configure firewalls, monitor network traffic, troubleshoot connectivity issues, and protect enterprise infrastructure from cyber threats. Security tools such as firewalls, SIEM platforms, endpoint protection, and Zero Trust solutions depend heavily on IP Address visibility to detect and prevent unauthorized access.
Mastering IP Address concepts is a fundamental skill for careers in cybersecurity, networking, and cloud computing. It helps professionals analyze traffic flow, implement NAT, investigate security incidents, and design secure network architectures.
Key areas where IP Address knowledge is essential include:
- Firewall configuration and policy implementation
- Cybersecurity monitoring and threat detection
- Network troubleshooting and connectivity analysis
- Enterprise and cloud infrastructure deployment
For cybersecurity professionals, a strong understanding of IP Address plays a critical role in working with enterprise firewalls, SIEM tools, cloud security platforms, and Zero Trust architectures in 2026 and beyond.
In real-world enterprise environments and technical interviews, IP Address is one of the most frequently tested and practically used networking concepts. Learning it deeply builds a strong technical foundation and accelerates career growth in cybersecurity.
references: link
if you want more blogs read please visit technaga
Important Note: This article is based on hands-on cybersecurity experience and research from reliable sources. While every effort has been made to ensure accuracy, you should validate the information based on your specific environment and security requirements before applying it.



1 thought on “IP Address: 12 Essential Concepts Ultimate Guide 2026”