We live in a world where the internet is part of almost everything we do daily. From paying bills to saving photos, we depend on it for nearly everything.
The internet has made life simpler, faster, and more convenient. But this convenience also brings a big question — how safe are we while doing all these things online every day?

Cybersecurity means protecting computers, mobiles, and networks from hackers or attacks. It helps keep our data, money, and personal information safe from theft or misuse in the digital world.
You can think of cybersecurity as digital protection for our online life — just like how we use locks, cameras, and passwords to keep our personal belongings safe in real life.

The Digital World and Its Dangers
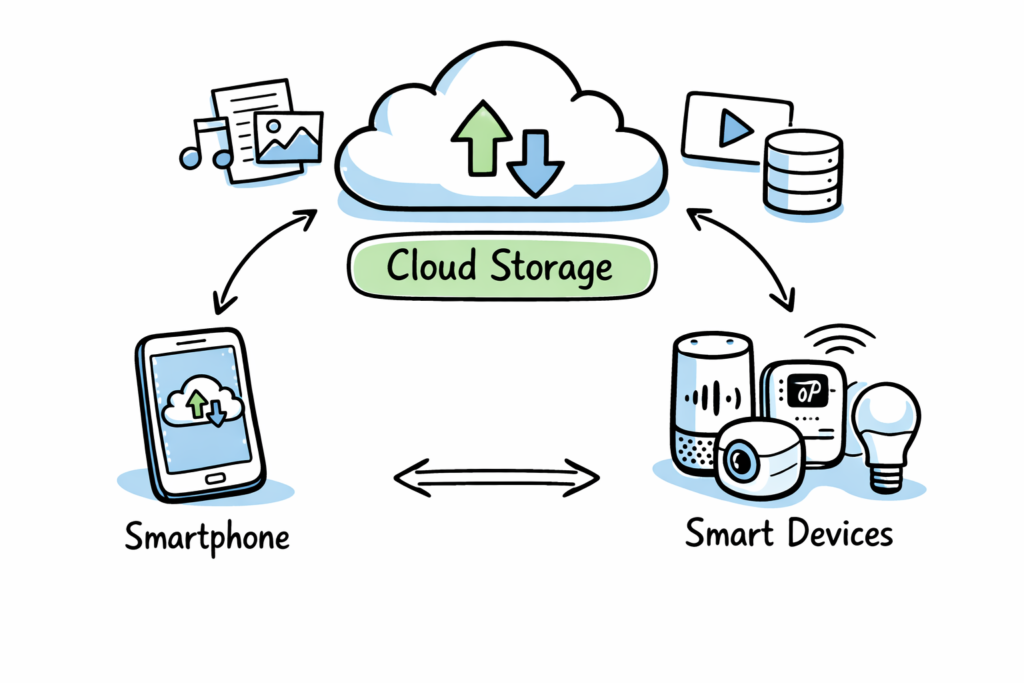
Technology has been growing very quickly over the last few years. Cloud storage, smartphones, and smart devices all help us, but they also increase the risk of online attacks.
Hackers don’t only target big companies anymore. They also attack small businesses and even individuals who don’t use proper protection or security awareness while using the internet.

There are now more cybercrimes than ever before — including ransomware, data theft, and identity fraud. Every year, companies lose millions due to weak cybersecurity systems and human mistakes.

The real loss isn’t only money — it’s also our privacy, trust, and the feeling of safety when we use online services or share information digitally in daily life.

Why Cybersecurity Matters for Everyone
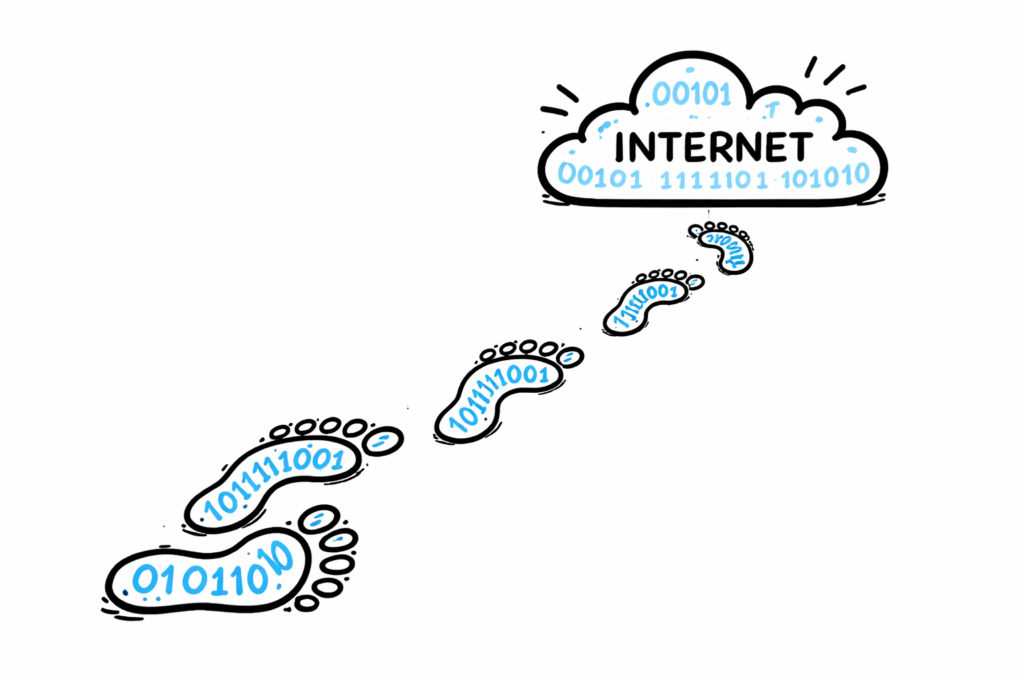
Many people still think cybersecurity is only for experts or companies. But today, every internet user needs basic protection because each of us leaves digital footprints everywhere online.
We connect to the internet for almost everything. Hackers can steal passwords, credit card numbers, or use fake websites to trick us into sharing important information without realizing it easily.

For companies, one attack can disrupt everything. A small mistake or ignored warning can cause loss of customer data, reputation, and money worth months or even years of hard work.

Governments are also making stricter laws about data privacy. For example, India’s DPDPA demands organizations keep user data safe or face huge fines for failing to do so.

So, cybersecurity is no longer optional. It’s an important part of every digital activity — both for personal safety and professional trust that affects everyone using the internet.
The Human Factor in Cybersecurity

Most cyberattacks happen because of human mistakes rather than technical failure. People often click unknown links, use weak passwords, or forget to update their devices regularly online.
Security awareness is one of the strongest protections. Learning how to spot phishing emails and using strong passwords reduces most common risks found while using digital systems every day.

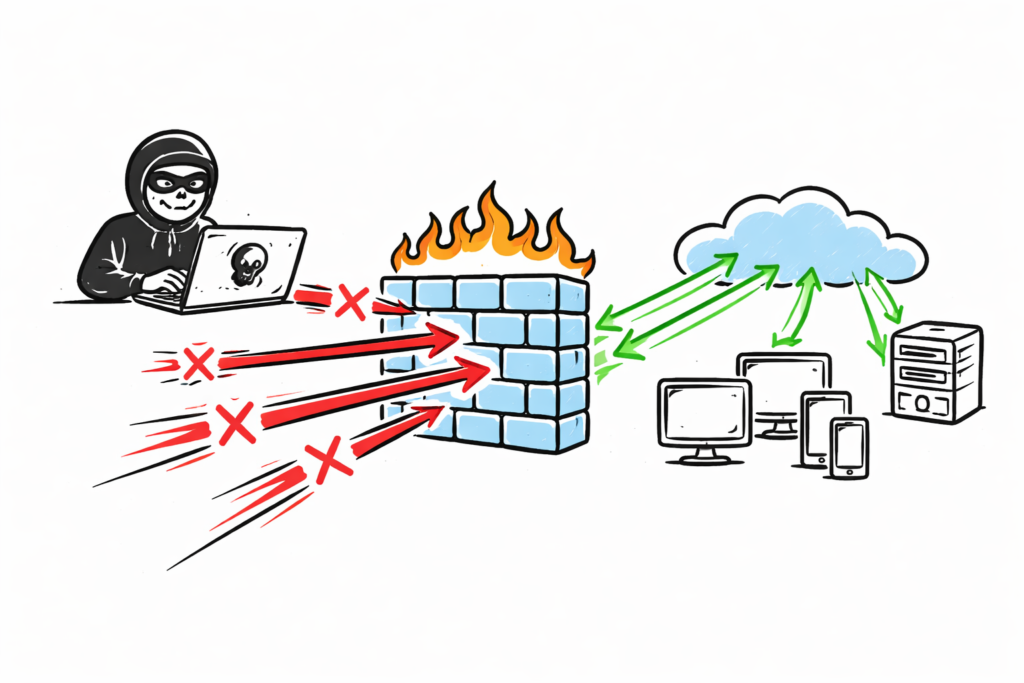
Cybersecurity isn’t just about software or firewalls. It’s also about changing habits, being alert, and developing safe online behavior across personal and professional online activities daily.

Everyone, from students to business owners, can make the internet safer. The key is to learn, stay alert, and use good cybersecurity practices wherever possible.
Main Areas of Cybersecurity
Cybersecurity has many branches. Each one focuses on different types of protection. Let’s look at the most important subdomains every beginner should know about.
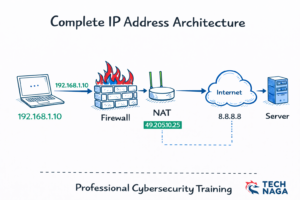
Network Security keeps internal systems and data protected from attackers. Firewalls and VPNs help stop unauthorized access and monitor traffic coming into and leaving a network. more info
Application Security ensures websites and apps are safe from bugs or misused code. Security testing helps developers close vulnerabilities before hackers try to find and exploit them.

Cloud Security protects data stored on online platforms such as AWS, Azure, or Google Cloud. It manages access and prevents data leaks or unauthorized sharing across locations.

Endpoint Security protects personal devices such as computers, tablets, and phones. Antivirus software and regular updates prevent viruses or spyware from causing harm to user systems.

Identity and Access Management (IAM) ensures only the right people can access specific files, apps, or information. It’s handled using passwords, fingerprint scans, or multifactor authentication.

Incident Response and Forensics comes in after an attack. These experts contain the threat, recover affected systems, and analyze evidence to understand how the attack happened inside.

Governance, Risk, and Compliance (GRC) deals with rules and policies. It ensures organizations follow global standards like ISO 27001 while managing security risks carefully and responsibly.

Operational Security (OpSec) focuses on daily data use inside companies. It prevents accidental leaks and stops employees from sharing sensitive information by mistake or carelessness.

Ethical Hacking and Penetration Testing involve testing security systems safely. Ethical hackers find weaknesses before criminals can exploit them, helping organizations improve their protection levels.

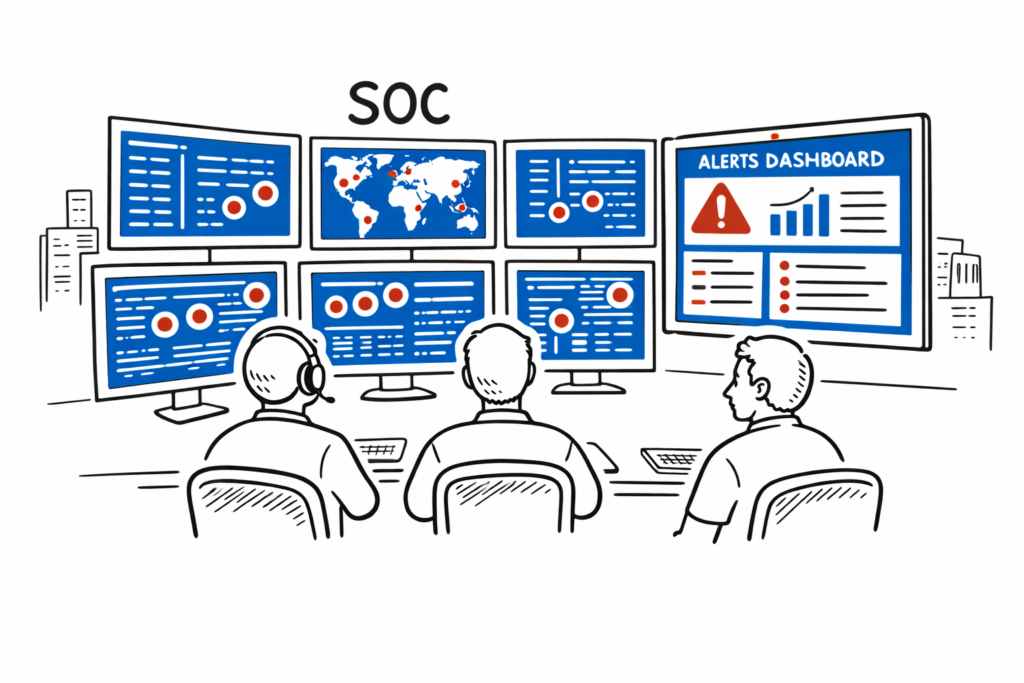
Security Operations Center (SOC) professionals monitor systems continuously. They detect suspicious activity, respond quickly, and use threat intelligence to prevent future attacks proactively.
Cybersecurity as a Career

Cybersecurity is one of the fastest-growing and most rewarding career fields today. Every company, school, or government sector needs skilled people to protect their data and systems.
You don’t need to be a coding expert to start. Curiosity, logical thinking, and a willingness to learn are enough to begin a successful career in cybersecurity gradually over time.
There are many career options — from technical hacking jobs to security policy roles. Each one offers opportunities to learn, grow, and contribute to online safety efforts globally.

Certifications like CompTIA Security+, CEH, or CISSP can help. They act as proof of skills and open doors to good jobs around the world with competitive salaries and respect.
The more technology advances, the higher the demand for cybersecurity experts will grow. This makes it a great field for long-term stability and global opportunities for learners everywhere.

Final Thoughts

Cybersecurity is not just for businesses or IT professionals anymore. It affects everyone who uses a smartphone, computer, or any device linked to the internet daily.

A single careless action — like clicking a fake message — can lead to serious loss. Staying cautious and informed is the simplest way to avoid many online threats easily.
As the digital world grows bigger each day, cybersecurity becomes the foundation of trust. Without it, innovation, privacy, and progress can’t grow safely or confidently for the future.
So next time you go online, remember — every small safe step matters. You are not just using the internet; you are protecting a small piece of it every day.