Welcome to Tech Naga, your trusted source for cutting-edge cybersecurity and tech insights. In 2026, digital payments have become the lifeblood of the global economy, with the Unified Payments Interface (UPI) handling billions of transactions daily. However, as the ecosystem grows, so do the threats. Understanding UPI fraud is no longer just for cybersecurity professionals; it is a critical survival skill for every digital citizen.
In this comprehensive guide, we will break down exactly what UPI is, explore the complex architecture behind modern digital scams, and provide you with enterprise-level security controls to protect your hard-earned money. Let’s dive in.
What is UPI and How Does It Work?
Before we can defeat a threat, we must understand the system it attacks.
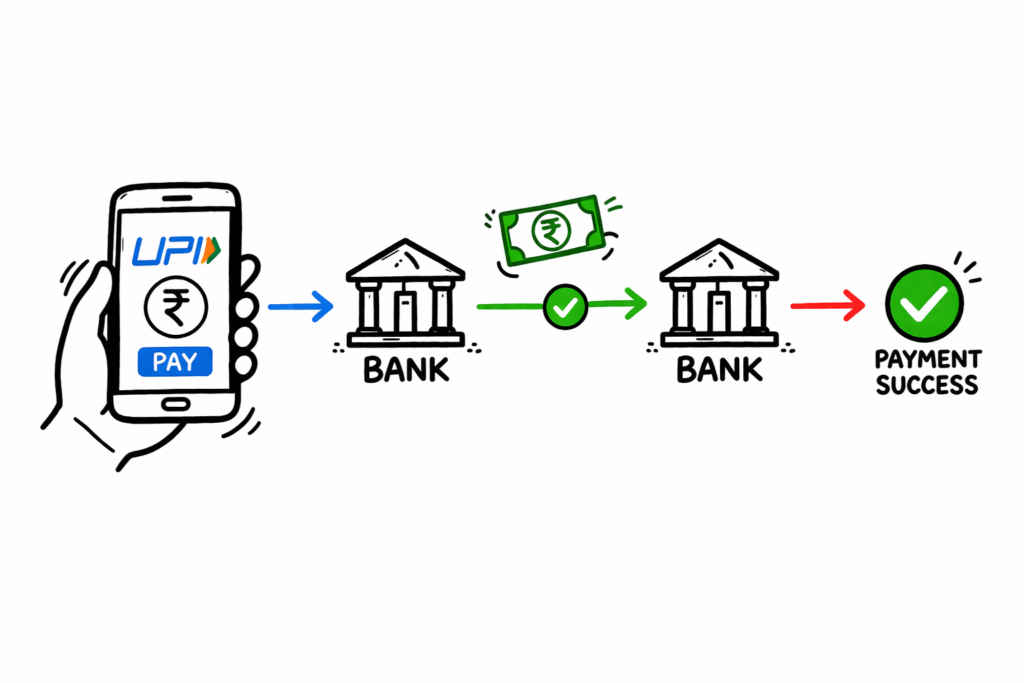
Definition Box: Unified Payments Interface (UPI) is a real-time, single-window payment system developed by the National Payments Corporation of India (NPCI). It facilitates instant inter-bank peer-to-peer (P2P) and person-to-merchant (P2M) transactions using a mobile device, eliminating the need to enter bank details repeatedly.
The Core Concept of Unified Payments Interface
UPI operates on top of the Immediate Payment Service (IMPS) infrastructure. Instead of sharing sensitive account numbers and IFSC codes, users create a Virtual Payment Address (VPA) or UPI ID (e.g., yourname@bank). This acts as a financial e-mail address.
The UPI Transaction Flow (Step-by-Step)
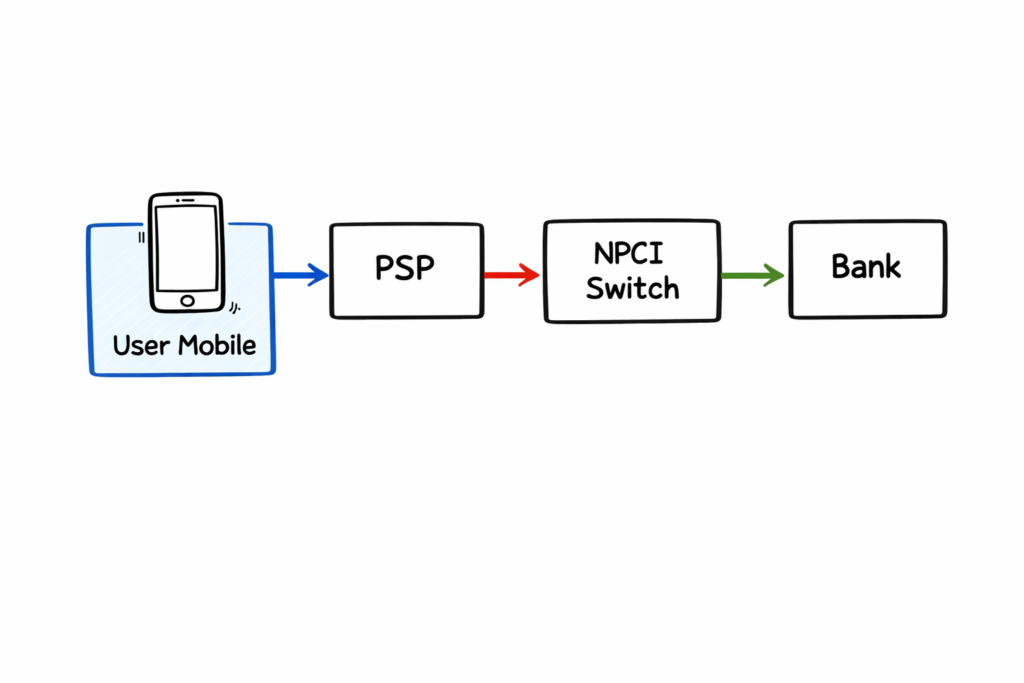
To understand where security breaches happen, look at the standard flow:
- Initiation: The sender opens a UPI app (Google Pay, PhonePe, Paytm) and enters the receiver’s UPI ID or scans a QR code.
- Routing: The request goes to the sender’s Payment Service Provider (PSP).
- Verification: The NPCI switches the receiver’s VPA.
- Authentication: The sender enters their secret UPI PIN.
- Settlement: The sender’s bank debits the account, and the receiver’s bank credits the amount instantly.
How UPI Fraud Works in 2026
Despite the heavy encryption at the backend, UPI fraud thrives by exploiting the weakest link in the cybersecurity chain: human psychology.
Social Engineering and Phishing
Hackers rarely try to brute-force the NPCI servers. Instead, they use social engineering. They manipulate victims into willingly sharing sensitive information or authorizing malicious transactions. They create a false sense of urgency (“Your bank account will be blocked!”) or extreme excitement (“You’ve won a lottery!”).

Screen Sharing Scams
In 2026, scammers increasingly use remote-access tools. They pose as customer support agents and convince users to download apps like AnyDesk or TeamViewer. Once installed, the scammer can see the victim’s screen, capture banking OTPs, and observe the UPI PIN being entered, leading to devastating financial loss.

UPI Fraud Architecture Explained
To truly grasp the mechanics of UPI fraud, we must look at its technical blueprint.
The Technical Blueprint of a Scam
The architecture of a typical UPI scam bypasses the encrypted API layers of the banking network entirely.
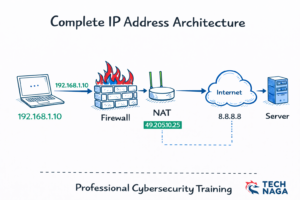
- Layer 1 (The Hook): SMS gateways or WhatsApp API scripts send out millions of phishing links containing spoofed domains (e.g., https://www.google.com/search?q=paytm-kyc-update.com).
- Layer 2 (The Interface): A fake web interface that mirrors a legitimate payment app. It utilizes deep-linking (upi://pay?pa=scammer@bank&pn=Merchant&am=50000) to force open the user’s actual UPI app.
- Layer 3 (The Execution): The user, believing they are logging in or receiving money, enters their UPI PIN. The NPCI switch processes this as a legitimate, user-authorized transaction.
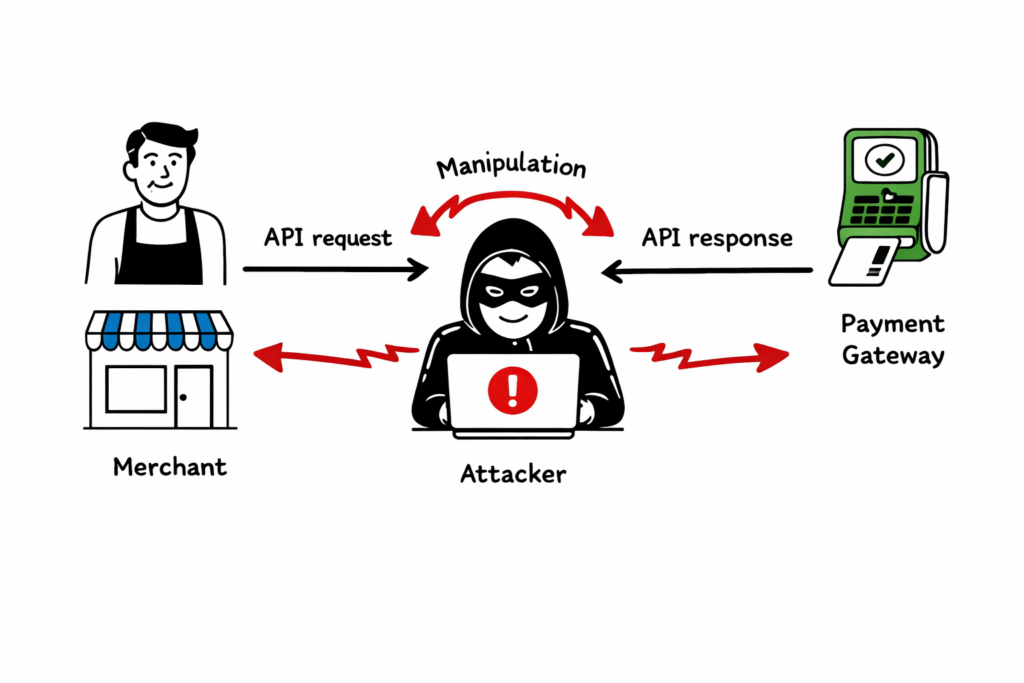
Payment Gateway & API Vulnerabilities
While rare, enterprise-level vulnerabilities do occur. If a merchant’s payment gateway is poorly configured, attackers can intercept the callback URLs. They manipulate the API response to make a failed transaction appear successful to the merchant, allowing them to steal digital goods or services without actual payment.
Types of UPI Frauds to Watch Out For
Fraudsters are highly creative. Here are the most prevalent types of UPI fraud today.
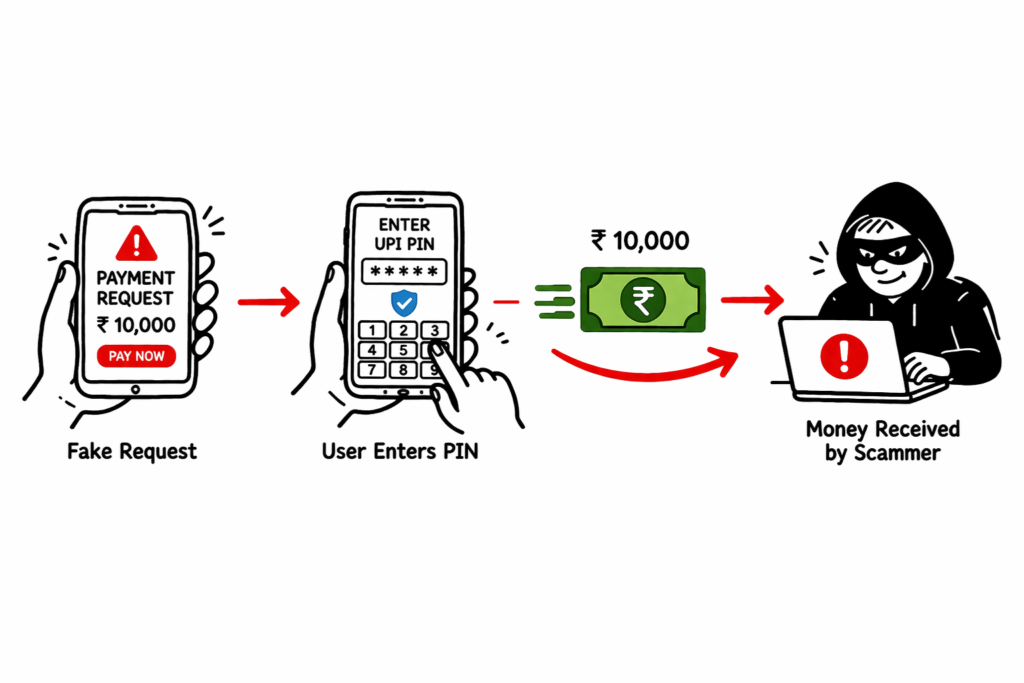
Collect Request Fraud
This is the most common tactic. The scammer sends a “Collect Request” to your UPI app. They call you, claiming they are sending you money for an item you listed online, and tell you to “enter your PIN to receive the funds.”
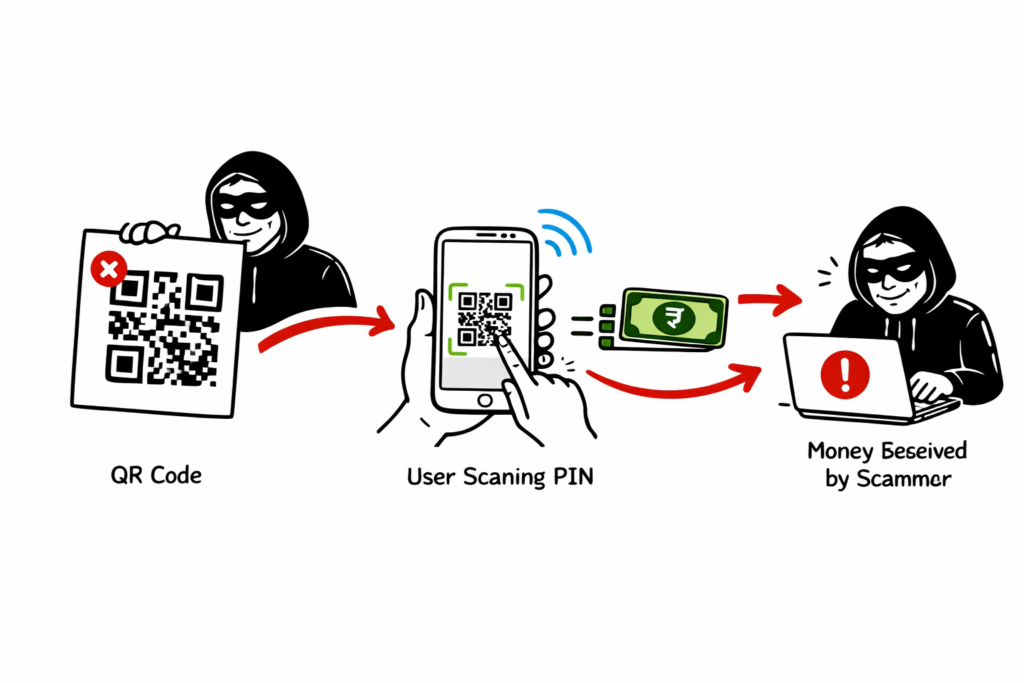
Fake QR Code Scams
Scammers paste their own malicious QR codes over legitimate merchant QR codes at local shops or petrol pumps. When you scan to pay the merchant, the money goes straight to the scammer’s account.
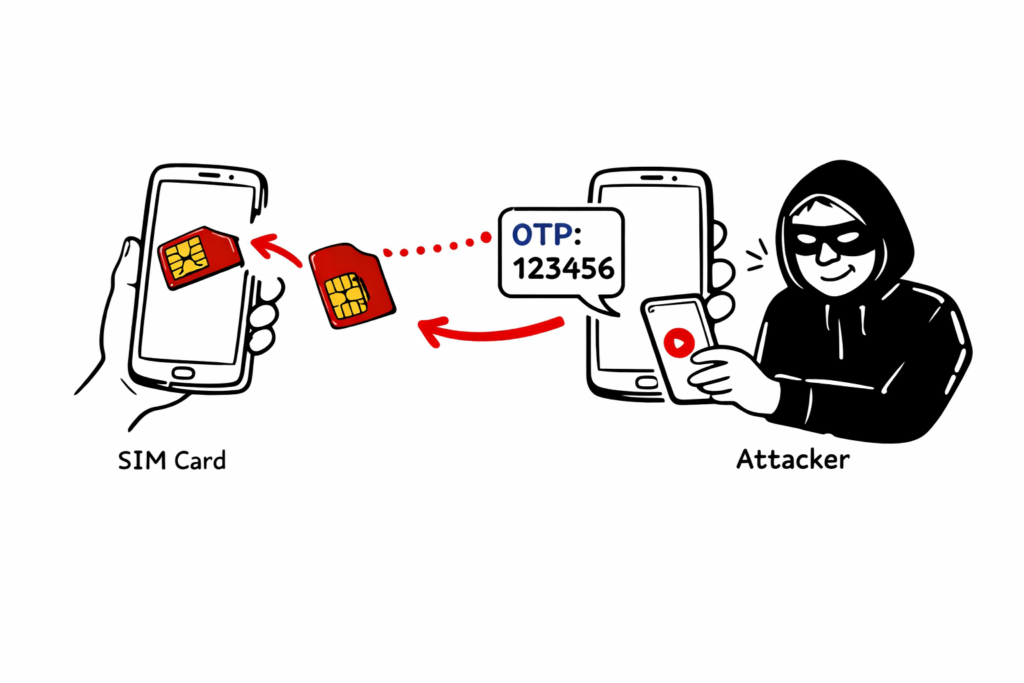
SIM Swapping and Device Binding Exploits
Attackers use fake ID proofs to trick telecom operators into issuing a duplicate SIM card of your number. They then register a new UPI app instance on their device. Because they control your SMS, they easily bypass device-binding OTPs.
Real-Life Scam Examples & Enterprise Cases
Let’s look at how these theories play out in the real world.
The Customer Care Number Scam
A user searched for “Zomato customer care number” on Google. Fraudsters had optimized a fake number using black-hat SEO to appear at the top of the search results. When the user called, the scammer sent a link to process a “refund.” Clicking the link triggered a pre-filled UPI payment of ₹10,000. In a panic, the user entered their PIN, losing the money instantly.
Enterprise-Level Incident: The Fake Merchant Onboarding
In a notable B2B scenario, a syndicate registered fake shell companies and onboarded them as verified merchants with a leading Payment Aggregator. Because “Verified Merchants” have higher daily transaction limits, the scammers used these accounts to funnel millions in stolen funds from retail victims before the aggregator’s risk algorithms caught the anomaly.
Advantages and Limitations of UPI Security
UPI is an incredibly robust system, but it is not magic.
Key Security Advantages
- Two-Factor Authentication (2FA): Every transaction requires device binding (What you have) and a UPI PIN (What you know).
- No Account Exposure: You never have to reveal your bank account number or IFSC code to third parties.
- Tokenization: Highly sensitive data is tokenized when communicating between the PSP and NPCI.
Inherent Limitations
- Irreversibility: Because settlement is real-time, recovering funds after a successful UPI fraud transaction is notoriously difficult.
- Device Dependency: If your phone is stolen while unlocked, the security model is severely compromised.
Enterprise-Level Security Controls for UPI
How do massive fintech companies protect their ecosystems? They utilize advanced, enterprise-grade architectures.
AI-Driven Fraud Monitoring Systems
Banks use Machine Learning models to calculate risk scores in milliseconds. If a user who normally spends ₹500 at local grocery stores suddenly tries to transfer ₹1,00,000 at 3:00 AM to a newly created VPA, the AI flags it, holds the transaction, and requires secondary biometric verification.
Multi-Factor Authentication (MFA) at Scale
Beyond just OTPs, enterprises in 2026 use behavioral biometrics. The app analyzes the angle at which you hold your phone, your typing speed, and touch pressure. If a scammer takes over your account via remote access, the behavioral biometrics will not match, and the session will be terminated.
Common Mistakes Users Make & Best Practices
Even with AI security, user awareness is the ultimate firewall.
The “Entering PIN to Receive Money” Myth
- Mistake: Believing that you must enter your UPI PIN to receive money.
- Truth: Your UPI PIN is ONLY used to send money or check your balance. You will never need a PIN to receive funds.
Proven Best Practices for Users
- Verify the VPA: Always double-check the receiver’s name before hitting send.
- Set Transaction Limits: Lower your daily UPI transfer limits in your banking app.
- Never Share Screen: Never download apps like AnyDesk under instructions from strangers.
- Use UPI Circle Wisely: With the new UPI Circle delegation features, only delegate secondary payment rights to strictly trusted family members.
Future Trends in UPI Fraud (2026 and Beyond)
As technology evolves, so does the nature of UPI fraud.
AI-Generated Voice Scams (Deepfakes)
In 2026, fraudsters are utilizing AI to clone the voices of your friends and family. You might receive a frantic phone call that sounds exactly like your sibling asking for an urgent UPI transfer for a medical emergency.
Offline UPI (UPI Lite X) Exploits
With UPI Lite X allowing offline transactions via NFC up to ₹5000, physical proximity attacks are rising. Attackers with modified NFC readers attempt to bump against users in crowded subways to initiate unauthorized offline deductions.
Interview Insights: Cybersecurity Expert Q&A
We sat down with a top FinTech Security Architect to discuss the realities of digital payments.
Q: In technical interviews, candidates are often asked how they would secure a UPI payment gateway. What is the right answer?
A: “A strong answer involves defense-in-depth. You must mention payload encryption, API rate limiting, IP whitelisting, velocity checks, and implementing automated reconciliation scripts that run hourly to detect ledger anomalies.”
Q: What is the biggest challenge in fighting UPI fraud today?
A: “The speed of the network. IMPS is immediate. By the time a victim realizes they’ve been scammed and calls the bank, the money has already bounced through three different mule accounts and been withdrawn as crypto or cash.”
Frequently Asked Questions (FAQ)
Can I get my money back if I am a victim of UPI fraud?
Yes, but time is critical. You must report the fraud to your bank and the National Cyber Crime Reporting Portal immediately (within 2-4 hours) to freeze the destination account.
Does UPI Lite require a PIN?
No. UPI Lite allows pin-less transactions for small amounts. This makes it convenient but requires you to keep your phone physically secure.
Are biometric UPI payments safe?
Yes, linking your FaceID or Fingerprint to your UPI app adds a robust layer of security that is extremely difficult for remote hackers to bypass.
Conclusion
The digital economy offers unparalleled convenience, but it demands constant vigilance. UPI fraud relies heavily on panic, greed, and lack of awareness. By understanding the underlying architecture of these transactions, recognizing the red flags of social engineering, and implementing the enterprise-level best practices outlined by Tech Naga, you can secure your financial future.
Remember, technology is only as secure as the person operating it. Never share your PIN, stay educated on the latest 2026 scam trends, and share this knowledge with your friends and family. Stay safe, and stay secure with Tech Naga!
if you want more blogs: visit technaga.com
National Payments Corporation of India (NPCI)
Note: The information shared in this article is based on my hands-on cybersecurity experience and research from multiple reliable sources. While I aim to provide accurate and practical guidance, readers should validate the information based on their specific environment and security requirements.